 This essay traces the historical roots of light as both a metaphor for knowledge and a means of control, and questions the relevance of this legacy for age of Internet phenomena such as Anonymous and Wikileaks. The talk was given at the conference Digital Light: Technique, Technology, Creation organized by Sean Cubitt, Daniel Palmer, Les Walkling, Jane Button, and Alex Gibson on 19 March 2011 at the University of Melbourne.
This essay traces the historical roots of light as both a metaphor for knowledge and a means of control, and questions the relevance of this legacy for age of Internet phenomena such as Anonymous and Wikileaks. The talk was given at the conference Digital Light: Technique, Technology, Creation organized by Sean Cubitt, Daniel Palmer, Les Walkling, Jane Button, and Alex Gibson on 19 March 2011 at the University of Melbourne.
The concept of light has no independent meaning in contemporary physics. Light is just a particular swath of wavelengths on the electromagnetic spectrum, nestled snugly between infrared and ultraviolet radiation. So-called "digital light" is even more an arbitrary category, since the light that shines from our laptops and smart phones starts out as voltage differentials on a hard drive. If the word "light" is to have any scientific significance, then it is distinguished not by any of its intrinsic physical properties, but by the biological fact that humans can see it.
Despite its irrelevance to physics, Euroethnic culture inherits from Enlightenment metaphysics a deep-seated sense that light is the emblem of truth rather than biological contingency. Rene Descartes said,
"Whatever is revealed to me by the natural light...cannot in any way be open to doubt." [1]
Even today, our language betrays our debt to Descartes' legacy. We need to attract a lot of "eyeballs" to our Web site, to maximize its "visibility." We have "sunshine" laws to guarantee government "transparency." I believe that the closer we look at our dependence on the metaphor of light as truth, the more we will see a political expediency hidden beneath it.
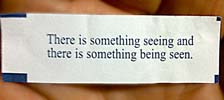 Last week I ate at an Asian restaurant and received this rather Orwellian fortune cookie:
Last week I ate at an Asian restaurant and received this rather Orwellian fortune cookie:
"There is something seeing, and there is something being seen."
As I sipped my green tea, I imagined the woman who stuck this fortune in the cookie, working in some factory under the watchful eyes of some overzealous night shift supervisor. Then I remembered that those human eyes are increasingly being replaced, according to the relentless logic of a globalized economy, by the more efficient digital eyes of a hidden security camera. In which case the fortune cookie really should have said:
"There is something seeing, but it is not being seen."I would propose that it is precisely this asymmetry that makes our unexamined metaphors of light so dangerous, and helps the powerful instill fear in the powerless.
The security cam watching the fortune cookie lady is of course a modern version of the Panopticon, Jeremy Bentham's notorious 1843 design for a maximum-security prison. Bentham's plans called for a central guard tower whose windows look out on an annular building divided into prison cells. Although impenetrable walls divide the inmates from each other, each cell has a window facing back at the tower as well as one on the opposite wall facing out into the world. The function of this window to the outside is not to give inmates a room with a view, but to backlight them against the light of day to make them all the more visible to the inspectors in the tower.
For their part, the inspectors employ Venetian blinds to ensure that inmates cannot tell at any given moment if they are being watched. Although Bentham had in mind the limited application of his design to prison architecture, Michel Foucault called the Panopticon "the diagram of a mechanism of power reduced to its ideal form," and went on to describe its influence in the nineteenth and twentieth centuries on the architecture of hospitals, workshops, and schools--in short, "whenever one is dealing with a multiplicity of individuals on whom a task or a particular form of behavior must be imposed." [2]
Here is a floorplan of the Panopticon. But it could also be the first draft of a floorplan for the 4 million-dollar new media center being built on my campus, where a newly proposed "information security policy" would require faculty to provide an inventory of everything on our laptops and ask permission to take them home at night. The fact that we can include the incompatible words "new media" and "center" in the same title show how persistent panoptic attitudes remain.
Of course, "digital" light is not a single sun in the sky shining down to provide chiaroscuro for Renaissance painters or backlighting for Panopticon wardens, but a dispersed array of handycams, Webcams, phonecams, predator drones, and face-recognition bots. While more dispersed, digital light is also less trustworthy, as we know from how easy it is to make a Photoshop fake. So if Descartes were alive today, he would have to write:
"Whatever is revealed to me by unnatural light...cannot in any way be trusted."
 If that's true, then why do we still ascribe to digital light the power to control that Descartes originally ascribed to natural light? As we move out of a broadcast paradigm and into a network paradigm, those metaphors of vision and its attendant radial model of information gathering and dissemination are increasingly irrelevant for a world lit not by a single light source in the heavens, but by a billion strands of interlinked fiber optics. The metaphor of light endures, I think, because it slides conveniently into a metaphysics of asymmetry, which happens to be a very convenient metaphysics for government officials, university administrators, CEOs, and anyone else who wants to stay in power.
If that's true, then why do we still ascribe to digital light the power to control that Descartes originally ascribed to natural light? As we move out of a broadcast paradigm and into a network paradigm, those metaphors of vision and its attendant radial model of information gathering and dissemination are increasingly irrelevant for a world lit not by a single light source in the heavens, but by a billion strands of interlinked fiber optics. The metaphor of light endures, I think, because it slides conveniently into a metaphysics of asymmetry, which happens to be a very convenient metaphysics for government officials, university administrators, CEOs, and anyone else who wants to stay in power.
At the limits of an illuminated landscape is the horizon. In the past, the horizon was where enemies came from, so you built lookout towers to see barbarian invaders before they got to you. The horizon was also where you escaped to, so the guardians of the Panopticon controlled the sight lines through which escaped inmates would try to flee.
Now that the backlit horizon of the Panopticon has been replaced with a backlit screen, we no longer see an invader before it is upon us. Paul Virilio has noted that in previous eras military control hinged on keeping the target always in sight. In the future, however, the means of control may not depend on visual contact. Reconnaissance can be replaced by a global Search, strikes by Search and Delete, invasion by Search and Replace, colonization by Search and Replicate.
As the offense abandons the Panopticon, so the defense must abandon the medieval tower. In Panoptic space, the higher the lookout tower, the better the control of information. In cyberspace, however, control is maintained not at a high level but at a low one: the lowest level of computer code is the most powerful, and data-miners reap profits by digging deep into code.
Information no longer radiates from a point outward in all directions, but follows diverse and sometimes multiple pathways to its destinations. If an inmate were missing from a given cell in an ordinary prison, the authorities would interrogate the next-door neighbors in the same cellblock, figuring they might be in on a conspiracy. Precisely to prevent such collaboration, Bentham designed walls between adjacent cells so that contiguous prisoners couldn't see each other. But in cyberspace, information's tendency to suffuse the local neighborhood is replaced by a tendency for information to shoot off in one or more discrete vectors.
So now governments and corporations interrogate nodes instead of neighbors, hoping to trace the routes information takes in the Internet age. That's why Egyptians organizing online protests in 2011 hid their activities using the Tor "onion router," designed to bounce network traffic through untraceable pathways. Unfortunately, not all netizens are as careful to hide their tracks. Bentham's guards locked inmates behind iron bars, while wardens of today's virtual enclosures have designed fishbowls that victims inhabit voluntarily; they're called Facebook accounts.
Architect Malkit Shoshan christened the 21st-century Panopticon spawned by the Internet the "Netopticon." A more accurate coinage would have been PanNetwork, since light is only an incidental medium for electronic networks. However, in clinging to an optical etymology the term Netopticon betrays the difficulty we have shedding the metaphor of light as information. In a NetOpticon, networks serve as just another conduit for light to bring information from the powerless to the powerful: advertisers mine Facebook, the FBI mines Twitter.
In a truly distributed network, however, information is not a commodity for privileged nodes to broadcast or trade privately; information is a property of the system. This is why light is such an inadequate metaphor for information in a network. [3] The most information on the planet sits where the sun doesn't shine, in the rhizomes and mycelia under the soil, in the nervous systems and brains of mice and men, in what neurologists call the "connectome." As Joline Blais argues, Enlightenment was about the trees--in Diderot's words, "encompassing each and every branch of human knowledge." Now it's about the roots. [4]
 Marshall McLuhan claimed in The Global Village that electronic networks are based on an acoustic, rather than an optical, world-view in that they permit overlapping, mutually compatible signals without a clear origin. Indeed, Bentham's first plan for the Panopticon had included an acoustic surveillance system with pipes leading from the cells to the central tower. The problem was that the prisoners could also hear what the inspectors were doing. Could Bentham's leaky network offer a prototype for a more liberatory Internet? Perhaps if we refuse the metaphysics that information is light bestowed by a higher power and hack some leaks into the Panopticon.
Marshall McLuhan claimed in The Global Village that electronic networks are based on an acoustic, rather than an optical, world-view in that they permit overlapping, mutually compatible signals without a clear origin. Indeed, Bentham's first plan for the Panopticon had included an acoustic surveillance system with pipes leading from the cells to the central tower. The problem was that the prisoners could also hear what the inspectors were doing. Could Bentham's leaky network offer a prototype for a more liberatory Internet? Perhaps if we refuse the metaphysics that information is light bestowed by a higher power and hack some leaks into the Panopticon.
Go underground
The disorganized mob of bored geeks known as Anonymous have terrorized YouTube, the Australian government, and the Mubarek regime, and been named by CNN as a potential successor to WikiLeaks. Yet unlike political leaders who cherish the limelight, the primary weapon wielded by these guerrillas--apart from knowing enough JavaScript to be dangerous--is their studious application of technologies that render their identities invisible. They've poked leaks into security firms and governments, while remaining too dispersed to be pinned down themselves.
Blind them with light
In 1993 Jennifer Ringley of JenniCam had chosen the opposite strategy to hack the Panopticon: by setting up a Webcam and leaving it on 24/7 for seven years, she flooded the Web with unedited images of her everyday moments. [5] One year before Ringley retired her Webcam, Hasan Elahi became Ringley's successor as a more political strategy in response to US government insinuations that he was a terrorist. Rather than conceal his private information from Big Brother, Elahi decided to leak everything about his life publicly, via a Web site that obsessively documents every plane he takes, every hamburger he eats, every toilet he pees in.
Unfortunately, while these floodlights on quotidian behavior may have been radical in their day, the subsequent launch of Facebook and Twitter showed that most netizens are happy to broadcast intimate details of their lives without political or aesthetic motivation, to the commercial benefit of data-miners.
Light up your path
Mobile technologies are like a Panopticon on wheels, which is why Richard Stallman won't even carry a cell phone. German Green party politician Malte Spitz took his carrier, Deutsche Telekom, to court to learn his carrier had recorded his GPS position 35,000 times in a six-month period. Google Street View even captured a privacy advocate stepping out of his office at the Electronic Frontier Foundation to sneak a cigarette.
In an evocative response, Ze Frank invited people to use Google Street Views to follow a remembered route they used to walk in childhood and then note down their emotional reactions. Frank's intervention is more targeted than the "flood everything" model of Ringley and Elahi, though of course his participants are just giving Google more information on themselves.
Heath Bunting's anamorphic photos designed to fool security cameras and fake-identity services like Tracenoiser both aim to chaff the network, distracting would-be data-miners with fake information. But those who fly close to the sun have to take care not to get burned. The Security Camera Players were a group of actors who acted out scenes for the benefit of security guards in front of cameras in public spaces, until one of their lead actors was himself compromised by a hidden camera even he didn't see.
Tunnel from light to dark
John Bell's Octris is a Virtual Reality version of Tetris that uses musical chords as cues for which falling puzzle pieces fit where. While originally designed with blind spatial engineer Nick Giudice as the audience, the work trains sighted viewers to listen for acoustic matches by slowly dimming the light as they level-up the game.
Light up the watchtower
Wikileaks may be the most infamous contemporary conduit of leaked information, but Steve Mann turned the tables on store clerk in a much more personal way back in 1997. Wearing his own custom-made sunglasses with a built-in hidden video camera, Mann asked a store clerk if she was bothered by the nearby surveillance cameras. In response to her platitude "if you have nothing to hide, they shouldn't bother you," Mann took out his own camera--at which point she protested his invasion of her privacy. Thanks to his secret recording, these two contradictory moments are caught on the same video.
Mann's SafetyNet is perhaps the most progressive hack of the Panopticon to date. In his model, concealed Wearcams netcast continuous video from the wearer not to the entire world, but to a geographically dispersed band of compatriots who could "sousveille" the wearer and intervene in the case of police brutality or personal injury. In giving one's friends, rather than an official police force, the responsibility of looking after a person, SafetyNet is less a strategy of turning a floodlight on Big Brother than handing flashlights to one's Little Brothers.
Dangle something shiny
Like those deep-sea anglerfish, Natalie Jeremijenko's project How Stuff Is Made offers bait that lure corporate maldoers into stepping into the light of their own accord. This wiki produced by Jeremijenko's students offers revelations about contemporary products that their manufacturers may not want public--such as the fact that shrimp farmers earn pennies per hour, American flags are made in China, and that the woman who stuffed my fortune into its cookie was quite possibly a Hispanic worker in Philadelphia.
To set the trap, Jeremijenko's students email the companies represented on the site and invite them to correct any factual errors. Marketing mavens can hardly resist the temptation of whitewashing a wiki to suit their PR needs, as studies of corporate influence in Wikipedia suggest. In this case, the edits made to this wiki are visible in the page's history, and Jeremijenko built the site with plans to highlight such changes in order to draw attention to corporate coverups.
Point out cracks in the lightbulb
I'll end by pointing out a limitation of the metaphysics of light that I'm particularly conscious of during this teleconference, namely time zones. [6] For the "always on" Internet, time zones are an anachronism, a carryover from an era in which all human activity was governed by circadian rhythms--that is, the sun's traversal across that neighborhood's slice of the globe. In the 19th century, the telegraph and railroad expanded the need for a consistent nonlocal time; time zones solved the contradiction between the global time of networks and the local time of sunlight by insisting that "it's 10am your time but 7pm my time." And today, the fact that we appear to be seeing each other at the same moment via Skype seems to assuage that discomforting anachronism.
But a little thought shows the imposition of time zones on a continuous sphere to be completely illogical: an exercise in continuity that produces one of the most discontinuous artifices imaginable, the International Dateline--a sort of self-declared time machine in which stepping a meter east or west propels you forward or backwards 24 hours in time.
On a more personal note, today, March 19th, happens to be my birthday. Unfortunately for me, you can celebrate and I can't: although it's Saturday March 19th in Melbourne, it's still Friday March 18th in Maine. So today's conference has put me in the awkward position of being 48 and 49 years old at the same time--a rather uncomfortable feeling that demonstrates the extent to which we are willing to give up bedrock assumptions about time in order to cling to cherished metaphors of light. [7]
Thankfully, I had already foreseen this awkward "moment" thanks to my fellow curator and presenter Steve Dietz, who for his exhibition Edge Conditions exhibited a work in 2006 by artists Jon Thomson & Allison Craighead. Their installation, a simple Webcam of the sky in Oceania shown in San Jose, artfully underscored the contradictions inherent in applying the paradigm of light to the Internet under the title "Light from Tomorrow." [8]
Thank you.
Some of the concepts in this talk were originally introduced in "Do We Want Convergence?" in Artbyte (New York) 2, no. 2 (Summer 1999), pp. 26-27, archived online.
1. Rene Descartes, Meditations on First Philosophy. 3, AT 7:38, quoted in the Stanford Encyclopedia of Philosophy, http://plato.stanford.edu/entries/descartes-epistemology/, accessed on 26 March 2011.
2. Michel Foucault, Discipline and Punish: The Birth of the Prison, (New York: Random House:1977), p. 205.
3. From the standpoint of quantum physics, even light is capable of entanglement, an experimental result that calls into question whether light is a broadcast medium at all.
4. Joline Blais in conversation with the author, 17 March 2011.
5. The Wikipedia page on Jennifer Ringley, in one of the site's more memorable phrases, notes that "CNET hailed JenniCam as one of the greatest defunct websites in history," citing the Internet Archive.
6. This talk was originally given over Skype from a location in Maine to the conference on the opposite side of the globe in Melbourne. Melbourne was 15 hours ahead of Maine, and hence 7pm in Maine was 10am the next day in Melbourne.
7. For very different reasons, Einstein made a similar choice to privilege light over time, and Special Relativity was the result.
8. I'm grateful to Craig Dietrich for reminding me about this piece.






